Resource Capacity Planning
Identify and Resolve Resource Bottlenecks!
Definitive Pro provides a time-phased resource management capability by enabling resource managers to enter their team’s capacity over time (by month) and to estimate their resources for each project. The project manager uses the resource estimates to estimate the cost of the project. They also enable the portfolio manager to review and analyze the data at the portfolio and enterprise level, identify resource conflicts and bottlenecks, and act to alleviate the resource contention. The resource data is also used by the optimizer to ensure that the recommended portfolio of projects can be resourced.
The Resource Capacity Planning Process
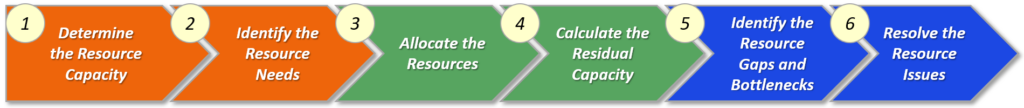
| Step | Step Name | Description |
|---|---|---|
| 1 | Determine the Resource Capacity | Fr each functional area, determine the total capacity based on the number of employees/team members. Then, subtract the resources required to support all overhead activities and non-discretionary work. Take into consideration planned retirements, attrition, and new hires. |
| 2 | Identify the Resource Needs | For each discretionary project, identify the required resources over time. |
| 3 | Allocate the Resources | Based on the priorities of the discretionary projects, assign the resources to the projects. Ensure that no functional area is over allocated. |
| 4 | Calculate the Residual Capacity | Analyze the resource plans (capacity vs. allocated) by project and by functional area. |
| 5 | Identify the Resource Gaps and Bottlenecks | Identify any situations where there are small resource gaps that may be addressable, and where adjusting the timing of projects may enable resources to be smoothed. Establish a strategy for addressing resource capacity needs. For example, determine if it is appropriate to hire or contract for additional resources, while taking into consideration the time to hire and the procurement acquisition lead time, as appropriate. |
| 6 | Resolve the Resource Issues | Resolve the short-term resource conflicts and bottlenecks. In addition, address the longer-term resourcing needs that may arise with emerging technologies and changing cyber security landscape. |